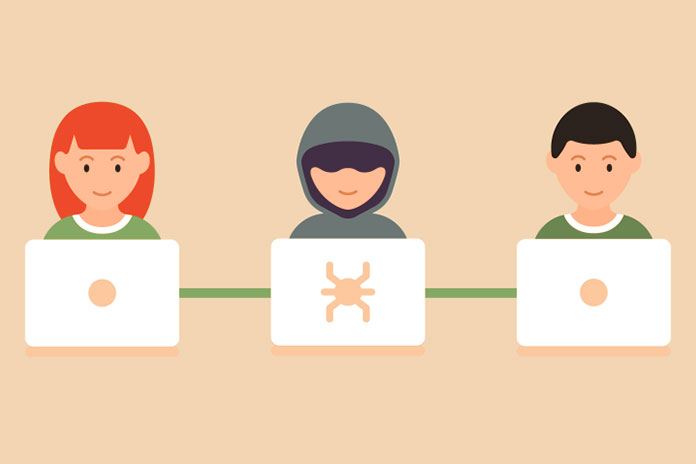
Man-in-the-middle is a cyber attack that allows the cyber attacker to intercept and manipulate internet traffic. Here are all vulnerable devices and a guide to protect us. An intruder who enters our online communications. This is an attack known as man-in-the-middle, whose main goal is to steal our information.
It is a particularly insidious threat because it is silent: most of the time, the victim does not realize anything.
What Is Man-In-The-Middle Attack?
Man-in-the-middle translates as a man in the middle and is a cyber threat that allows the attacker to intercept and manipulate internet traffic that the user believes is private. More specifically, in the case of a man-in-the-middle attack, the attacker puts himself in the middle between two entities trying to communicate with each other: a client (the victim) and the server router.
In this way, it not only manages to intercept sent and received messages. But, if he wants, he can also modify them or pretend to be one of the two parties. In the offline world, we can imagine him as someone who puts fake invoices in our mailbox and then tries to collect payment for them.
What Are The ways Man-in-the-middle can attack us?
Almost any type of internet connection can be compromised through a man-in-the-middle attack.
Man-in-the-wifi: One of the oldest and most common ways is to compromise the wifi network. Usually, the most exploited are the public ones found in airports, hotels, or bars. But the attack can also occur within the home network. Crackers have several ways to “get in the way”: they can create a fake wifi node (called a “bad twin”) that simulates a legitimate access point to trick us. Another way is to monitor web traffic on an unencrypted connection and look for session cookies to hijack our account. Or, an attacker could change their home wifi password to gain access.
Man-in-the-mobile: We are always connected, thanks to the smartphone. In recent years, a great opportunity for cybercriminals is increasingly trying to infect mobile devices with man-in-the-middle attacks to intercept all SMS traffic. The main goal is to bypass the two-factor authentication that protects our financial institution accounts and beyond. In this way, the cracker can obtain the various authentication codes sent by message.
Man-in-the browser: Also known as the banking trojan, the man-in-the-browser attack involves malware installed on the victim’s device. Once operational, it can modify online transactions made, for example, to a bank. In practice, the browser will show us the correct transaction, while in reality, another one is being made.
Man-in-the-IoT: The Internet of things is now a reality. The objects connected to the Internet are thousands: from TVs to washing machines, passing through thermostats. All intelligent, but also all potentially vulnerable. “Internet of threats” was baptized by Eugene Kaspersky, founder of the famous and homonymous IT security company. Among the threats to which smart devices are exposed, there is no shortage of man-in-the-middle attacks that can be used to intercept very sensitive data concerning us and collected from every device connected to the web.
Man-in-the-app: Apps aren’t immune either. In this case, the cracker can forge the security certificate that apps and sites use to ensure communications between them and the user are secure. A tactic that allows him to communicate directly with the application and steal all the data we have given him.
How to Defend against Man-in-the-middle Attacks?
On the consumer front, there are several measures that we can all take to protect ourselves:
- Never use unencrypted or free wi-fi access points to carry out sensitive transactions;
- Make sure you are using the encrypted version of the websites, checking that the URL starts with HTTPS;
- Set a password for home wi-fi WPA2 encryption and change the default password with a better one (at least 15 characters recommended);
- Always update antivirus and operating system to the latest version;
- Do not visit websites when the browser alerts us of a problem in their security certificate;
- Enable two-factor authentication in all our most important accounts, such as email;
- Avoid using your work or home computer for transactions. An ad hoc one is preferable.